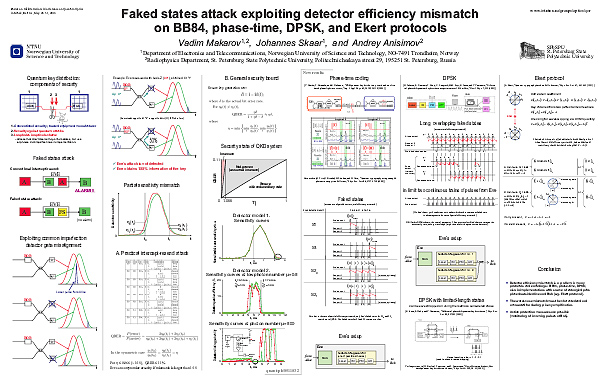

The left half of the poster is based on quant-ph/0511032; the right half presents ideas now included into
You can download the poster: PDF (1.1MB) | JPEG (1.5MB)
Also, you can download a slide presentation with exactly the same content as the poster: PowerPoint (2.0MB; to see animations, run the presentation in the Slide Show mode) | PDF (1.7MB)
Errata
— In the rightmost column, in the description of the Ekert protocol, in the first equation labelled “Correlation coefficient”, all five instances of
— In the rightmost column, in the description of faked states for the Ekert protocol, the numerical values of probabilities for sending them should be swapped. The correct probabilities are