 For the last / current year course materials, please see the main page.
For the last / current year course materials, please see the main page.
2023
Lecture 1 (introduction).
Lecture 2 (components of quantum-optical systems).
Lectures 3 and 4 were done on the blackboard.
Lecture 5 (measurements in quantum mechanics).
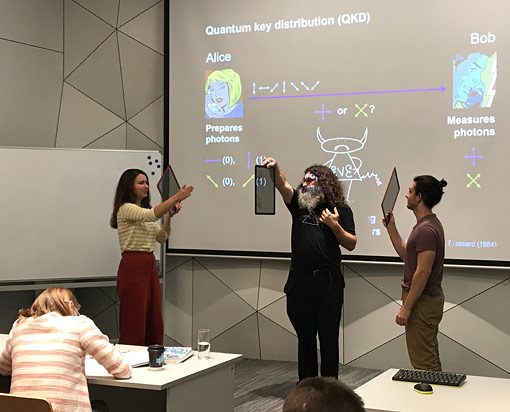
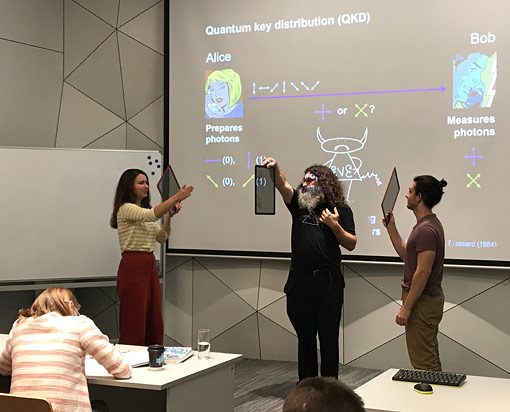
Lectures 6 and 7 (quantum key distribution).
Lectures 8–11 were done on the blackboard.
Lecture 12 (hacking attacks).
Lecture 13 (detector control attack), journal paper J.-G. Ren et al., “Ground-to-satellite quantum teleportation,” Nature 549, 70 (2017).
Lecture 14 (source distinguishability; certification), journal paper M. Lucamarini et al., “Overcoming the rate–distance limit of quantum key distribution without quantum repeaters,” Nature 557, 400 (2018).
Course program
Topics for written part of the exam
Topics for oral part of the exam
2022
Lecture 1 (introduction). For those who have missed it, you can watch a similar introductory lecture in Russian or in English.
Lecture 2 (components of quantum-optical systems).
Lectures 3 and 4 were done on the blackboard.
Lecture 5 (measurements in quantum mechanics).
Lectures 6 and 7 (quantum key distribution).
Lectures 8–11 were done on the blackboard.
Lecture 12 (hacking attacks).
Lecture 13 (certification and audit), journal paper J.-G. Ren et al., “Ground-to-satellite quantum teleportation,” Nature 549, 70 (2017).
Lecture 14: journal paper M. Lucamarini et al., “Overcoming the rate–distance limit of quantum key distribution without quantum repeaters,” Nature 557, 400 (2018).
Course program
Topics for written part of the exam
Topics for oral part of the exam
2021
Lecture 1 (introduction). For those who have missed it, you can watch a similar introductory lecture in Russian or in English.
Lecture 2 (components of quantum-optical systems).
Lectures 3 and 4 (basics of quantum optics to application examples).
Lectures 5–11 were done on the blackboard.
Lecture 12 (security model of QKD, Trojan-horse attack).
Lecture 13 (detector control attack), journal paper J.-G. Ren et al., “Ground-to-satellite quantum teleportation,” Nature 549, 70 (2017).
Lecture 14 (source distinguishability; certification and audit), journal paper M. Lucamarini et al., “Overcoming the rate–distance limit of quantum key distribution without quantum repeaters,” Nature 557, 400 (2018).
Course program
Topics for written part of the exam
Topics for oral part of the exam
2020
Lecture 1 (introduction). For those who have missed it, you can watch a similar introductory lecture in Russian or in English.
Lecture 2 (components of quantum-optical systems)
Lecture 3 (basics of quantum optics)
Lecture 4 (quantum key distribution)
Lecture 5 was done on the blackboard without recording and included a simulation of BB84 and B92 protocols.
Lecture 6 was done on the blackboard without recording.
Lecture 7 was done on the blackboard and video recorded.
Lectures 8&9 were done on the blackboard and video recorded.
Lecture 10 was done on the blackboard and video recorded.
Lecture 11 (security model of QKD, Trojan-horse attack) was video recorded.
Lecture 12 was done on the blackboard and video recorded.
Lecture 13 (detector control attack) was video recorded, journal paper J.-G. Ren et al., “Ground-to-satellite quantum teleportation,” Nature 549, 70 (2017).
Lecture 14 (source distinguishability; certification and audit), journal paper M. Lucamarini et al., “Overcoming the rate–distance limit of quantum key distribution without quantum repeaters,” Nature 557, 400 (2018).
Course program
Topics for written part of the exam
Topics for oral part of the exam
2019
Lecture 1 (introduction)
Lecture 2 (quantum optics)
Lectures 3&4 (quantum optics, QKD)
Lecture 5 (QKD implementations)
Lectures 6–9 were done on the blackboard.
Lectures 10&11 (quantum hacking, Trojan-horse attack), journal paper L. Lydersen et al., “Hacking commercial quantum cryptography systems by tailored bright illumination,” Nat. Photonics 4, 686 (2010).
Lecture 12 (detector control attack), journal paper J.-G. Ren et al., “Ground-to-satellite quantum teleportation,” Nature 549, 70 (2017).
Lecture 13 was done on the blackboard, journal paper M. Lucamarini et al., “Overcoming the rate–distance limit of quantum key distribution without quantum repeaters,” Nature 557, 400 (2018).
Lecture 14 (source distinguishability; certification and audit)
Topics for the oral exam